How a global miner rebuilt their SOX management across every entity, and what other US organizations can learn

Sarbanes-Oxley (SOX) programs rarely fail because teams do not know what the controls are. They fail because execution gets lost across entities, sites, and process owners, and the “truth” ends up scattered across spreadsheets, Visio maps, and email threads.
That was the reality for one global diversified miner we worked with. Their controls framework existed, but day-to-day control execution tracking, testing follow-up and reporting were creating avoidable friction, especially at scale.
Company bio snapshot
- Industry: Diversified mining, global operations
- Regulatory driver: Sarbanes-Oxley (SOX) internal controls requirements
- Scope: Entity-wide controls framework, process maps, control execution tracking, testing, and remediation workflows
- Employees: 21,000+
The challenge: Sarbanes-Oxley (SOX) controls were scattered
If you’ve lived through a SOX cycle, you know the pattern. The RACMs exist. The process maps exist. The controls are “documented.”
But the reality of whether they’re being executed, by the right people, in every entity, on time, is buried across spreadsheets, inboxes, and version-controlled chaos.
That’s where this global diversified miner found itself. And it’s the same place a lot of US organizations end up when SOX has to work at scale.
They needed to:
- Create a single source of truth for RACMs and process maps
- Get out of spreadsheet survival mode and cut the admin drag of manual tracking
- Make ownership real, with clear accountability for every control across every entity
- Track control execution, not just control design on paper
- Make reporting usable, so testing status and follow-up could be seen instantly, not rebuilt for every committee cycle
Bottom line: they had to move from “we can prove this if we chase it down” to “we can run SOX like an operating system.”
The SOX management CoreStream GRC: bring process, risk and execution into one system
Once the miner was clear on the real problem, the solution was not another round of documentation. It was a structural change: connect process, risk, and control execution in one system so the framework could actually operate day to day.
CoreStream GRC was configured around 3 practical shifts:
1) One connected controls framework (no more disconnected artifacts)
Instead of Risk and Control Matrixes (RACMs) in one place and process maps in another, everything was linked:
- Processes, risks, and controls connected end-to-end
- Process maps tied directly to the controls framework, so the “why” and the “what” stayed aligned
- A complete audit trail of updates and changes, which matters in SOX environments where traceability is non-negotiable
2) Ownership you can see, not just assign
SOX accountability breaks when ownership is vague. Therefore, your software setup must make it explicit:
- Ownership assigned at the framework level (who owns the control)
- Ownership assigned at the monitoring level (who is responsible for testing, follow-up, and remediation tracking)
A good check is to ask yourself if you could answer the uncomfortable question fast: who is accountable for this control in this entity right now?
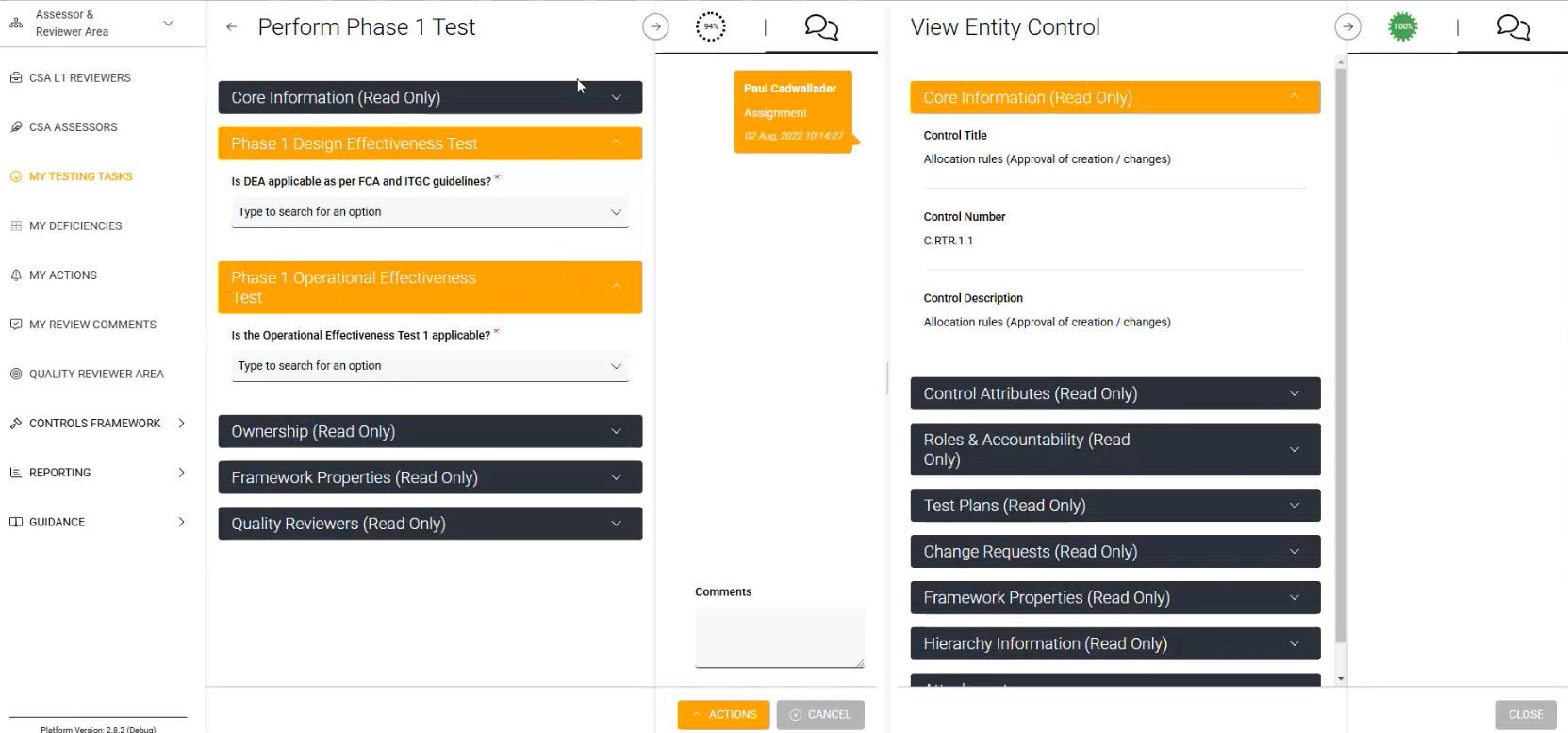
3) Workflow-driven execution, testing, and remediation (built for real life)
This is where Sarbanes-Oxley (SOX) stops being theoretical:
- Integrated workflows for control execution
- Structured workflows for control testing
- Built-in workflows for remediation and follow-up, so issues do not die in email thread
And because everything was live in one place:
- Real-time dashboards with filtering and drill-down replaced quarterly reporting scrambles
- Leaders could see progress, bottlenecks, and repeat issues without waiting for someone to compile it manually

Outcomes from using CoreStream GRC software: less spreadsheet drag, more SOX-ready clarity
With the single system of record in place, the miner achieved:
- A single source of truth for the control framework and process maps, replacing spreadsheets and disconnected Visio maps
- Improved efficiency in meeting Sarbanes-Oxley (SOX) requirements, with easier monitoring of control testing and remediation follow-up
- Clear accountability: ownership across the control framework and testing meant individuals were directly responsible for execution and closure
- Reduced administrative overhead in tracking items to completion and compiling management information, freeing time for higher-value work
This outcome mirrors what independent market feedback repeatedly highlights: when teams move off Excel-driven GRC, they stop spending days assembling reporting and start using live dashboards to run the program.
“Clients moving from Excel and PowerPoint into CoreStream GRC have seen immediate benefits: Days of manual report prep replaced by real-time dashboards and committee packs at the click of a button.”
Michael Rasmussen, GRC Pundit and GRC 2020 founder
Why good SOX management matters (especially for US organizations)
Sarbanes-Oxley (SOX) is not just something you “get through” once a year. In the US, it’s a live test of whether your controls program is actually running, or whether you’re just producing evidence on demand.
At a practical level, strong SOX management is the difference between:
- standardizing control expectations across every entity, not letting each team interpret controls their own way
- proving execution consistently, without last-minute chasing for evidence
- assigning ownership with zero ambiguity, so there’s no hand-waving when something slips
- surfacing issues early, before they turn into repeat findings, escalations, or uncomfortable audit committee conversations
That’s why this miner’s change matters. The idea was straightforward, but the execution is where most organizations fall apart:
Stop treating SOX like documentation management.
Start treating it like controls execution management.
Want to apply this to your SOX program?
If you’re dealing with any combination of:
- RACMs and process maps scattered across teams,
- control testing follow-up that lives in email,
- remediation that slips because ownership is unclear, or
- reporting that takes days instead of minutes,
then the pattern is the same.
CoreStream GRC can help you build a controls operating model that scales across entities, with workflow-driven execution tracking, testing, remediation, and real-time reporting.
Learn more about our controls management solution
-

CASE STUDY: South Western Railway
Reinventing rail compliance: how South Western Railway kept obligations under control through re-nationalization Contracts change. Ownership changes. Reporting lines change. However, what does not change is the impact risk can have on a business. Obligations must be tracked, updated, evidenced, and reported. And if your Governance, Risk & Compliance (GRC) platform cannot flex with the business change, teams fall back to outdated methods; spreadsheets, inbox chasing and hoping nothing gets missed. South Western Railway…
-

CASE STUDY: COI GRC 2020 solution perspective
The client stories behind Michael Rasmussen’s Conflict of Interest Management solution perspective for CoreStream GRC Introduction Michael Rasmussen, globally recognized GRC thought leader and former Forrester analyst who originally defined the Governance, Risk, and Compliance market, recently drafted his perspective on CoreStream GRC’s conflict of interest solution. For this analysis, Michael engaged with 3 organizations actively using the CoreStream GRC platform to manage conflicts of interest. While operating in…
-

CASE STUDY: Implementation success story
Raising the bar on Conflict of Interest management: CoreStream GRC’s high quality implementation services success story Everyone’s heard the horror stories of GRC implementations that drag on for months, sometimes years, with personnel moving in and out as people leave before the project is done. It’s no wonder risk and compliance teams cling to the devil they know. The fear of scope creep, decision paralysis, slipping timelines, and sheer…
FAQs for SOX controls management
Control design is the documented framework (RACMs, narratives, process maps). Controls execution is the day-to-day reality: who performs each control, when it happens, what evidence exists, and whether exceptions get remediated. Most SOX pain comes from execution being tracked across spreadsheets, email, and inconsistent local processes.
Because ownership and evidence get fragmented. Different entities interpret controls differently, testing follow-up lives in inboxes, and the “latest version” of RACMs and process maps becomes unclear. At scale, SOX fails less from missing controls and more from missing accountability, traceability, and repeatable workflows.
Yes, if the configuration connects process, risk, and control execution so updates happen as part of the work, not as an extra reporting step. The payoff is fewer manual trackers, less version confusion, and faster management information, because evidence, testing results, and remediation status sit in the same system.
Treat SOX like an operating model, not a documentation exercise. Standardize control expectations across entities, make accountability unambiguous, track execution and evidence continuously, and manage testing and remediation through workflows. That shift is what turns “we can prove this if we chase it down” into “we can show it instantly.”
Testing and remediation should be workflow-driven, with clear status, due dates, escalation paths, and evidence capture in one place. When remediation is tracked in email threads, issues stall and repeat findings become more likely. A structured workflow keeps exceptions moving until they are closed and provably closed.