How VinciWorks and CoreStream GRC help you build a risk-based, defensible third-party risk management program.
If you want a practical, easy to follow walkthrough of how to get third-party risk management right, this webinar is a great place to start.
What this webinar is about: connecting Governance, Risk and Compliance (GRC) with smarter third-party due diligence
Third-party risk has exploded. Supply chains are global, regulations are tightening, and every vendor relationship now carries financial, operational, cyber, ESG, and reputational exposure.
This joint VinciWorks and CoreStream GRC webinar cuts through the noise and shows what it actually takes to run a risk-based, repeatable, auditable third-party risk management (TPRM) program.
Hosted by Nick Henderson, Director of Learning and Content at VinciWorks, the session brings together:
- Gary Yantin, Director of Best Practice, VinciWorks
- Paul Cadwallader, GRC Strategy Director, CoreStream GRC
Plus, live Q&A with practitioners across legal, compliance, procurement and risk.
Across the hour, the speakers explain why third-party risk management (TPRM) is no longer a procurement checkbox and why organizations need an integrated, cross-functional approach to assessing, monitoring and managing vendor risk.
“The modern organization is the extended enterprise. There’s no longer a black-and-white border around your business.”
Paul Cadwallader, GRC Strategy Director, CoreStream GRC
Why to watch this conversation on third-party risk
If your teams feel overwhelmed by questionnaires, spreadsheets, sanctions check, scattered processes or growing regulatory pressure, this webinar gives you a clear path forward.
Here’s why it’s worth your time:
- Understand the extended enterprise and third-party risk context.
You’ll learn why the old idea of “our suppliers” is outdated. Most organizations now have hundreds or thousands of interconnected vendors, outsourcers, contractors and consultants.
“Even the smallest organization can have dozens of critical third-party relationships. In large organizations, it can reach 10s of 1000s.”
Paul Cadwallader, GRC Strategy Director, CoreStream GRC
- See how GRC integrates with third-party risk management (TPRM)
The speakers explain why vendor risk isn’t just a procurement activity. It needs governance, risk assessment, compliance checks, sanctions screening, privacy validation, and continuous monitoring.
- Learn how legal and compliance teams structure risk-based due diligence.
Gary walks through how law firms use structured risk-based due diligence to assess clients and suppliers and what other industries can borrow from that model.
- Move beyond questionnaires with modern due diligence tools and data sources.
The webinar shows why relying on vendor-submitted answers is no longer enough and how organizations are enriching due diligence with independent data, adverse media, cyber ratings, ESG ratings and more.
Ready to learn more?
If you want to strengthen your third-party risk management program and reduce reliance on spreadsheets and manual checks, this webinar is an excellent starting point.
Full transcription of the designing your GRC home webinar
0:00
Hello there and welcome to today’s webinar on managing the risks of doing business with third parties. I’m Nick Henderson, VinciWorks’ Director of Learning and Content. Today we’re joined by Gary Yanton, VinciWorks’ Director of Best Practice.
Hi Gary.
And also by Paul Cadwallader, Senior Vice President of Business Development at CoreStream GRC. Hello to you Paul.
0:25
Paul: Hi Nick. Great to be here and I’m looking forward to this session.
0:31
Nick: Great to have you both with us. We’re joined today by Paul from CoreStream GRC, who we work closely with. CoreStream GRC is a leading provider of risk management technology that helps organizations manage risk and compliance more efficiently and effectively. Since 2006 they’ve supported companies through consultancy and a flexible platform used by the BBC, NHS England, Great Western Railway, Network Rail, and more.
1:04
Paul is an experienced business leader and former Big Four partner who focuses on governance, risk, compliance, control, and assurance. We’re delighted to have him with us today.
1:29
We’re talking about third‑party risk management. Paul, briefly: how does Corestream help with managing the risks of doing business with third parties?
1:37–2:42 (Paul)
Our third‑party risk management solution uses our flexible platform. It has been described as agile, intuitive, value‑creating, effective, and adaptable. We tailor each client’s approach including process steps, workflows, risk models, questionnaires, and data sources.
Key features include segmentation of third parties based on risk, workflows triggering different assessment levels, questionnaires and data requests, sanctions and adverse‑media screening, deep‑dive due diligence using selected data sources, and dashboards showing overall third‑party risk rankings.
2:49
Nick: We also provide a full range of compliance e‑learning at VinciWorks, covering areas like anti‑money laundering, anti‑bribery, and more, including support for compliance departments within law firms.
3:23
Let’s look at how risk management interacts with third‑party risk management and vendor risk management. Paul, what do these concepts mean?
3:34–4:45 (Paul)
Modern organizations aren’t defined by physical walls anymore. They operate through an extended enterprise of third‑party and even “nth‑party” relationships; suppliers, vendors, outsourcers, contractors, consultants, temporary workers, agents, brokers, dealers, and partners.
Even small organizations may rely on dozens of third parties; large ones may rely on tens of thousands. These external relationships essentially become part of the organization, and managing risk across them is essential.
4:58–6:45 (Paul)
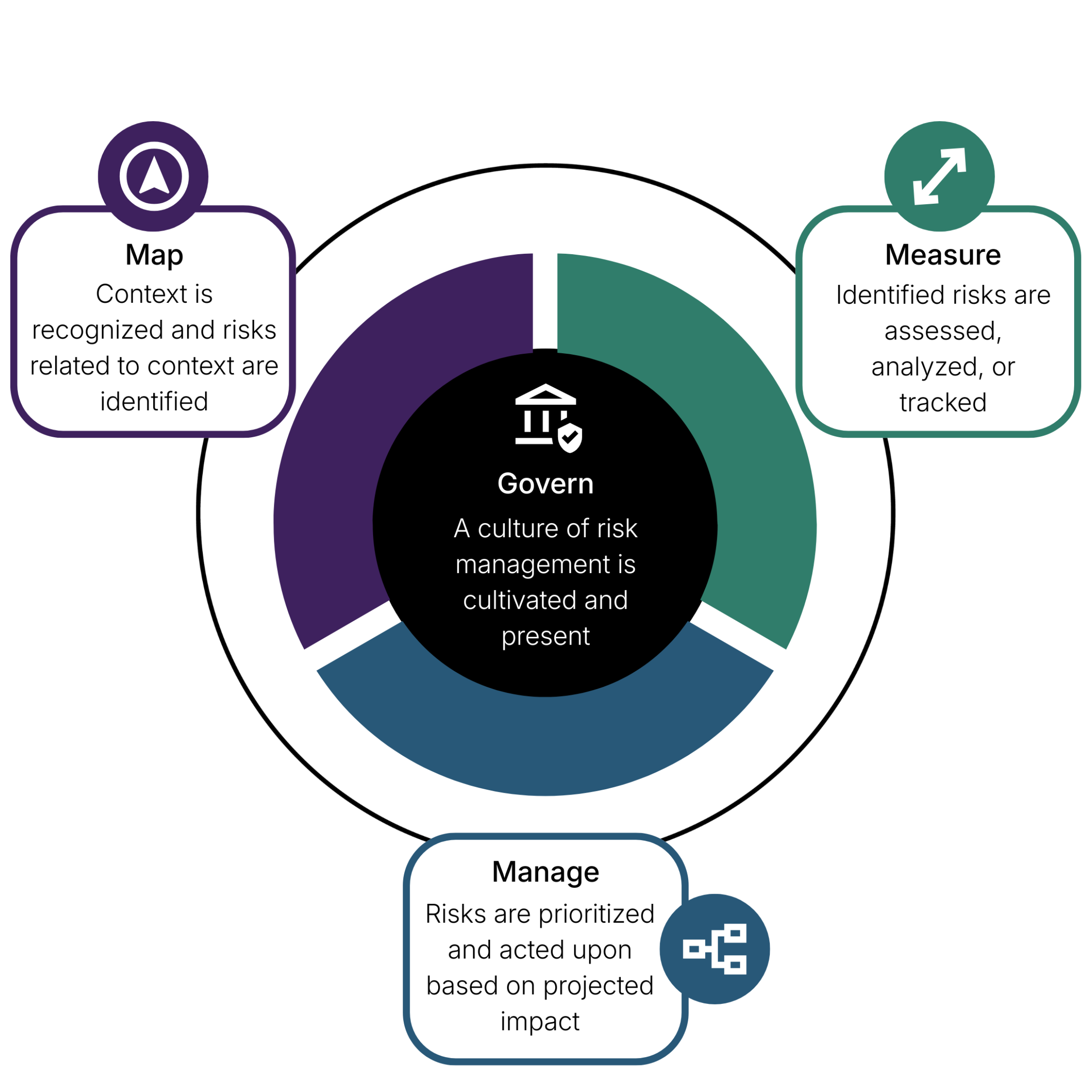
GRC—governance, risk management, compliance—is critical because businesses now rely on complex networks of third parties. Poor governance over third parties can lead to reputational, operational, ethical, or financial damage.
Organizations are held accountable for issues involving their third‑party partners, from ethics and privacy to safety, corruption, and environmental impact. Your ability to achieve business objectives depends on governing third‑party relationships effectively.
6:52
Nick: Gary, you’ve worked with the legal industry for many years. What can others learn from it?
7:04–8:52 (Gary)
Law firms are legally required to consider risk, so a risk‑based mindset is built in. They assess the nature of the client, the transaction, the source of funds, AML concerns, sanctions, and more.
That same approach applies to third‑party risk. No two relationships pose the same risk. A large international company isn’t the same as a small local supplier.
A risk‑based approach means tailoring due diligence: basic checks for low‑risk parties, more detailed analysis for medium‑risk, and extensive checks—including site visits—for high‑risk situations.
8:57
Nick: What risk factors should we consider with third parties?
9:03–13:19 (Gary)
Relevant factors include: location, industry sector, business background, identity, ownership structure, who else they serve (especially government customers), how critical their services are, and the nature of your relationship.
These should be considered holistically. One issue alone doesn’t automatically rule someone out, but patterns matter.
Low risk might involve basic internet searches and policy checks.
Medium risk might involve detailed policy review, interviews, references, and input from compliance, procurement, or legal teams.
High risk requires extensive data collection, audit trails, site visits, and continuous verification.
15:26
Nick: There’s a question from the chat: does something like purchasing stationery count as a supplier? What about a phone company?
Low‑risk suppliers such as large phone companies usually require minimal due diligence. It all depends on importance and risk level.
16:17
How do we actually undertake a risk assessment if someone is new to this?
16:17–21:12 (Paul)
You can’t take the same approach with every third party—it’s too time‑consuming.
A typical process:
- Check sanctions/watchlists and ownership.
- Assess the inherent risk of the product or service.
- Consider relevant risk domains (bribery, privacy, cyber, modern slavery, ESG).
- Use external data sources like adverse‑media screening, cyber ratings, and ESG ratings.
- Send targeted, dynamic questionnaires.
- Combine results to determine a final risk score.
- Use that score to decide: approve, mitigate, or reject.
22:25–23:23 (Paul)
Collect as much data as practical without creating friction. Use smart questionnaires plus external data to validate or enrich responses.
24:37–26:02 (Gary)
Always verify supplier information—don’t rely solely on questionnaires. Check ID documents, certificates, policies, references, and filings. Look for inconsistencies, which are often red flags.
27:03–29:02 (Gary)
Before making a decision, check for red flags such as: insufficient capacity, missing licenses, attempts to start work early, reluctance to provide certifications, unusual pricing, or pressure to rush a contract.
Ensure data is accurate, trustworthy, and complete.
29:44–30:45 (Gary)
If concerns remain, mitigate the risk by adding contract conditions, requiring controls, using ongoing monitoring, or delaying service start until requirements are met.
31:02
Nick: How far down the supply chain should risk management go?
31:02–34:06 (Paul)
It depends on your industry, regulations, and risk domains. Some areas, like modern slavery, require deeper‑tier visibility.
You can ask suppliers how they assess their own suppliers, request information on their vendors, or use AI‑based supply chain mapping tools.
34:26–37:27 (Nick & Gary)
Economic pressure, sanctions, the Russia–Ukraine situation, data privacy, cyber risk, and environmental issues all increase risk. Ongoing monitoring is essential.
38:59–40:04 (Gary)
Ongoing monitoring includes regular reassessments, performance indicators, certificate expiration checks, transaction monitoring, and continual sanctions/media checks.
40:18
Nick: That’s all we have time for today. Thank you to Paul from CoreStream GRC and Gary from VinciWorks. And thank you all for joining us.
FAQ on third-party risk management seminar
• Sanctions, geopolitical instability, modern slavery, cyber threats and ESG scrutiny now affect even small vendor relationships.
• Your risk exposure extends far beyond direct suppliers.
• Regulators expect deeper oversight across the full supply chain.
“Third party problems are your problems. They impact your brand, your reputation and your risk exposure.”
Paul Cadwallader, Strategy Director, CoreStream GRC
• Treating every supplier the same wastes resources and creates blind spots.
• Segment suppliers into risk tiers and tailor checks accordingly.
• Use structured scoring, red flag identification and holistic review.
“You cannot implement the same due diligence across every relationship. No two matters are the same.”
Gary Yantin, VinciWorks
• Questionnaires alone are limited. You need independent evidence.
• Pull data from watchlists, beneficial ownership checks, cyber ratings, ESG scores, adverse media and certifications.
• Look out for gaps or reluctance to provide proof.
“It is as much data as possible to get the best insight. But you must reduce friction and validate everything important.”
Paul Cadwallader, Strategy Director, CoreStream GRC
You’ll get a breakdown of key global regulations driving the need for structured due diligence:
Germany Corporate Due Diligence Act
Norwegian Transparency Act
Switzerland’s ESG due diligence laws
The EU Corporate Sustainability Due Diligence Directive (CS3D)
UK Modern Slavery Act expansion proposals
US actions on supply-chain integrity and forced labor risk
These rules increasingly require ongoing, evidence-based, risk-tiered oversight.
You will get value from this session if you are:
A Head of Risk or Compliance responsible for vendor oversight and governance
A Procurement leader trying to move beyond tick-box supplier onboarding
A Legal team member dealing with sanctions, contracts or regulatory exposure
An Internal Audit professional facing repeated findings around third-party controls
Data privacy or cybersecurity leads concerned about vendor security posture
A Corporate sustainability or ESG lead affected by supply-chain transparency laws
Or anyone responsible for managing suppliers, reducing operational risk or building a repeatable TPRM process